Content

DDoS attacks occur in various forms (e.g. ransom DDoS, carpet bombing, etc.) and regularly inflict serious damage on large and small companies all over the world.
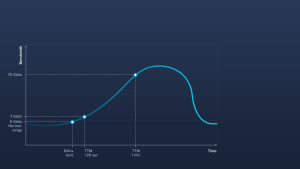
Attacks become more massive the longer they last
The impact of a DDoS attack is directly related to its duration. You can picture what happens in a graph. The line representing the attack is flat at the start but quickly rises over time as the attack grows in force. The growth curve increases rapidly after the first 20 seconds, by which time the attack has already seriously disrupted its target.
After about a minute, the curve becomes so steep that the attack is virtually unstoppable, and tangible consequences for the affected party are inevitable. At this point, the deployed infrastructure has either collapsed or is about to collapse. Web services suffer massive performance losses or, even worse, become completely unavailable.
Fast mitigation is relative
The above explains why mitigation of a DDoS attack should take place as quickly as possible. The next question is, how quickly a security solution should respond if an emergency arises. The obvious answer is as fast as possible. In reality, different attack patterns, such as UDP bandwith floods, TCP SYN floods and many others present protection solutions with different hurdles in terms of rapid response.
The challenge is to find an appropriate technology that not only protects against the most common types of attacks but does so in seconds, not minutes. Remember, after 20 seconds an attack becomes uncomfortable; after a minute it gets dangerous. Protection solutions that detect and mitigate DDoS attacks in less than 30 seconds are therefore optimal for enterprise use. First-class solutions detect known attack patterns directly and don’t let them penetrate the protective wall in the first place. This means that even large-scale attacks can bounce off the integrated protective measures – without even being noticed.
For this reason, the definition of a “fast” DDoS defense is relative. The first minute is critical in an attack and every second counts. The faster the DDoS protection solution acts, the more customers are protected from unwanted side effects. A time difference of 10 – 20 seconds may not sound like much, but in reality we‘re talking about potential damage that can cost you hard cash.
If mitigation is too slow, it gets expensive
Even in the early stages of a cyberattack, the consequences can be unpleasant – for example, the performance of your websites or web services may suffer. Companies that offer digital services to their customers should not be confronted with this scenario.
But things get even worse when a DDoS attack renders services inaccessible for minutes, hours, or even days. The economic damage in such cases is often massive, and the damage to the company’s image shouldn’t be underestimated. A rule of thumb says one minute of server downtime costs companies an average of 20,000 US dollars, but only in the rarest cases does the downtime cause only two or three minutes of restricted availability. Experience shows that most DDoS attacks last significantly longer, especially if no suitable protective measures are in place.
In addition, there are other possible follow-up costs to consider in the event of a critical DDoS attack:
– Easy to calculate hard costs
- Lost revenue
- Unproductive workers wages
- Fees / penalties
– Difficult to forecast hard costs
- Contractor costs
- Marketing costs
– Non tangible “soft” costs
- Lost business opportunities
- Decrease in stock value
- Driving fickle audience to competitor
- Lowering employee moral
- Eroding customer / business partner goodwill
- Bad publicity
For this reason, the best strategy by far is to prepare for denial-of-service attacks before they occur. Once they have begun, subsequent efforts are much more complicated and often have a much delayed effect.
Recovery isn’t instantaneous
If you are not prepared for a DDoS attack for various reasons and the potential worst case actually occurs, the desired system recovery is only possible again directly in the rarest of cases. Normally, you cannot assume that the attack will pass and everything will work again as before.
- From experience, databases take quite some time to be fully restored.
- The IT team will most likely have to put in a lot of overtime to restore the system.
- Recovering systems out of order / out of sync can cause queues to flood, cascading across multiple systems and trigger a secondary disruption, this is more likely the longer an attack persists and continues to fill ingestion queues. If it is non-critical data, spending a few hours manually purging queues and recovering systems in the correct order might be faster.
- Once routes / advertisements are dropped recovery is not immediate. Most transit providers will accept advertisements after several minutes of stability, but the free peering exchanges might take hours or longer, leaving you paying higher bandwidth costs and potential overage fees.
Leave nothing to chance in DDoS defense
Modern DDoS protection is a critical safeguard for any business, especially these days when the size and frequency of these attacks have increased exorbitantly. The key approach when choosing a protection solution is to compare the performance criteria of each option and pick the one that fits best with your business model.
A study by Frost & Sullivan, a leading global market research firm, recently reviewed the security technologies of leading DDoS vendors through extensive testing. For an overview of the results, you can download the study free of charge from us here.
[vc_btn title=”Download Whitepaper” link=”url://www.link11.com/en/benchmark/” el_class=”banner-green-btn commen-btn”]