Content

What are DNS Amplification Attacks?
DNS amplification attacks are a version of distributed denial-of-service attacks (also known as DDoS). These DNS amplification attacks use DNS servers as amplifiers.
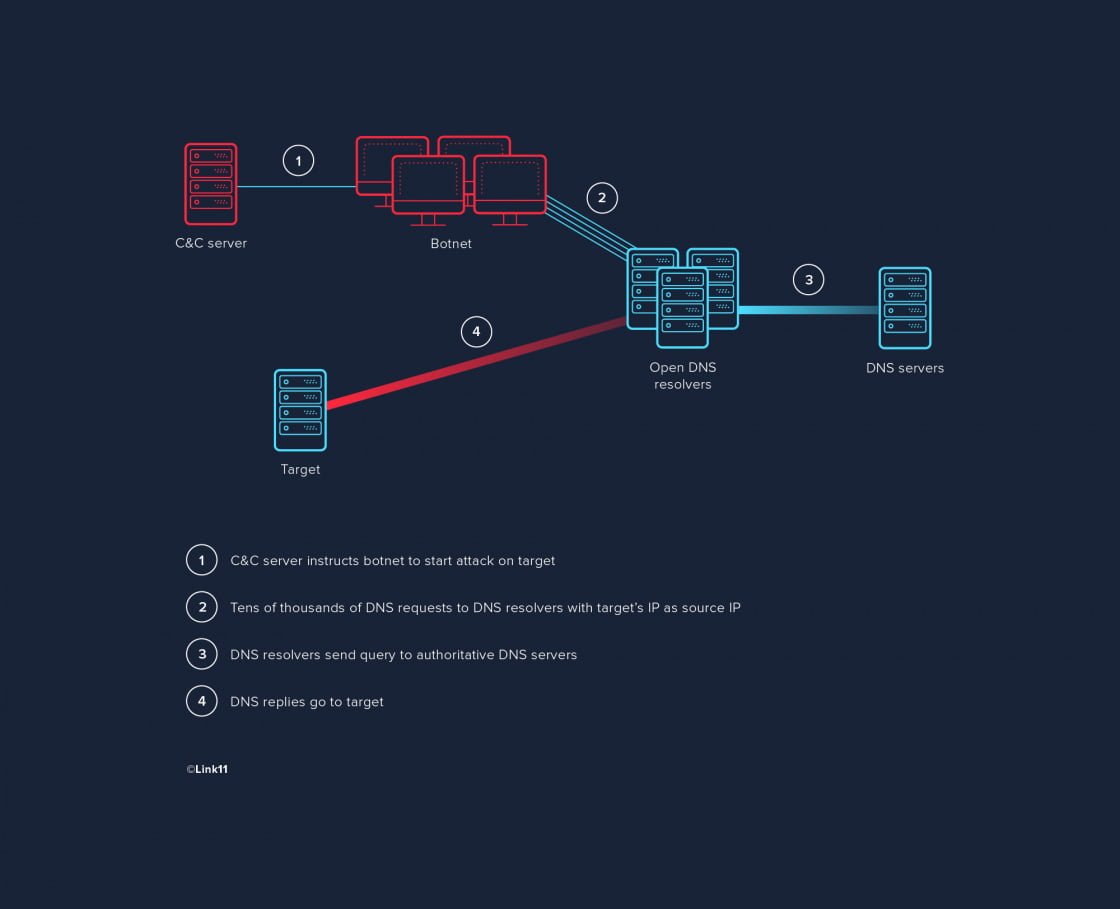
The attack itself is rather simple: the attacker has their botnet send tens of thousands of DNS requests to one or more public DNS resolvers. The bots use the target’s IP address as sender IP so that the DNS resolver’s replies are sent to the target instead of the attacker. That way, the DNS resolvers submit tens of thousands of replies to the target.
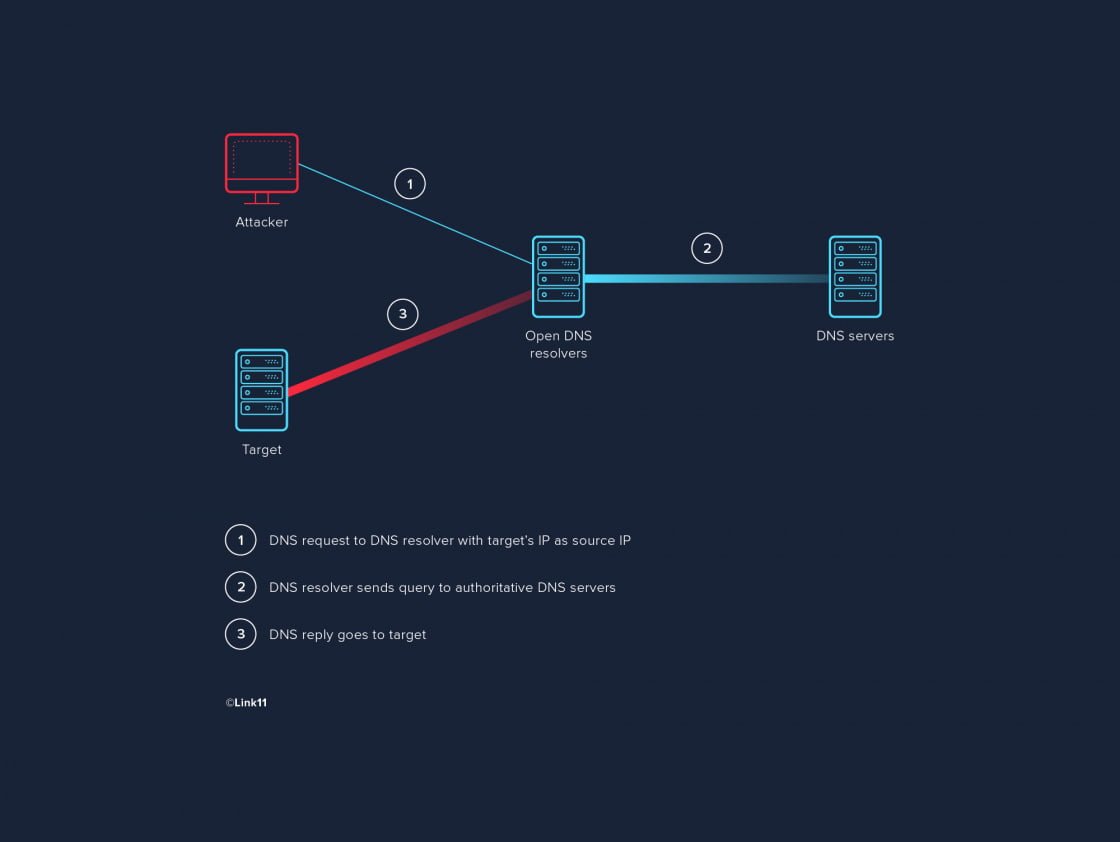
This is what the communication structure looks like (the example has just one bot attacking):
The attacker also exploits a specific feature of the DNS protocol: requests directed to DNS servers are often much smaller than their replies. A request with just a few bytes can trigger a reply with thousands of bytes. For example, a 50-byte request can result in a 5000-byte reply – an amplification factor of 100. This means that the attacker need only send a fraction of the data volume that is supposed to hit their target. A bot with a bandwidth of 10 Mbps can run an attack on the order of 1 Gbps, and an entire botnet can easily reach hundreds of Gbps.
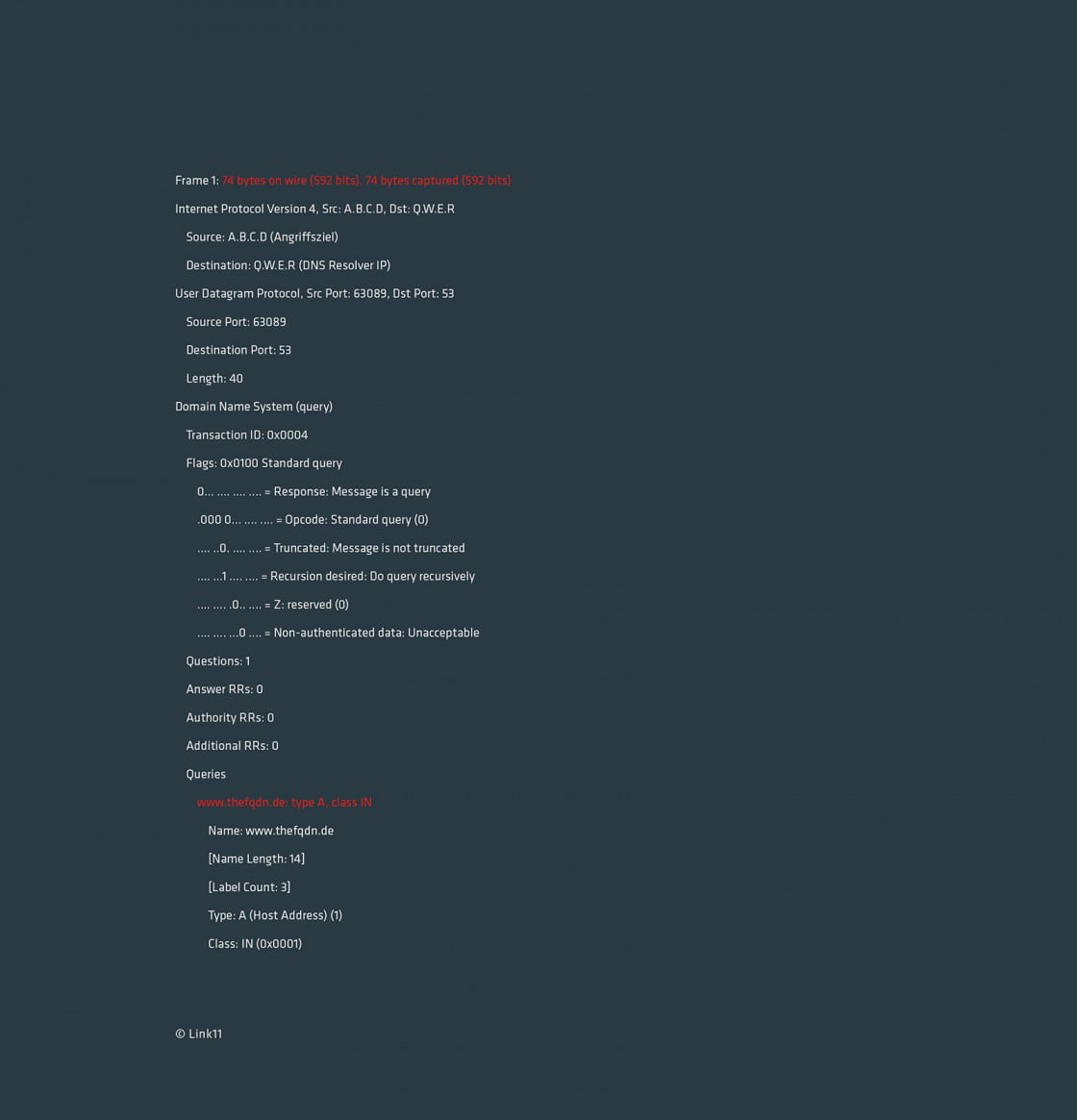
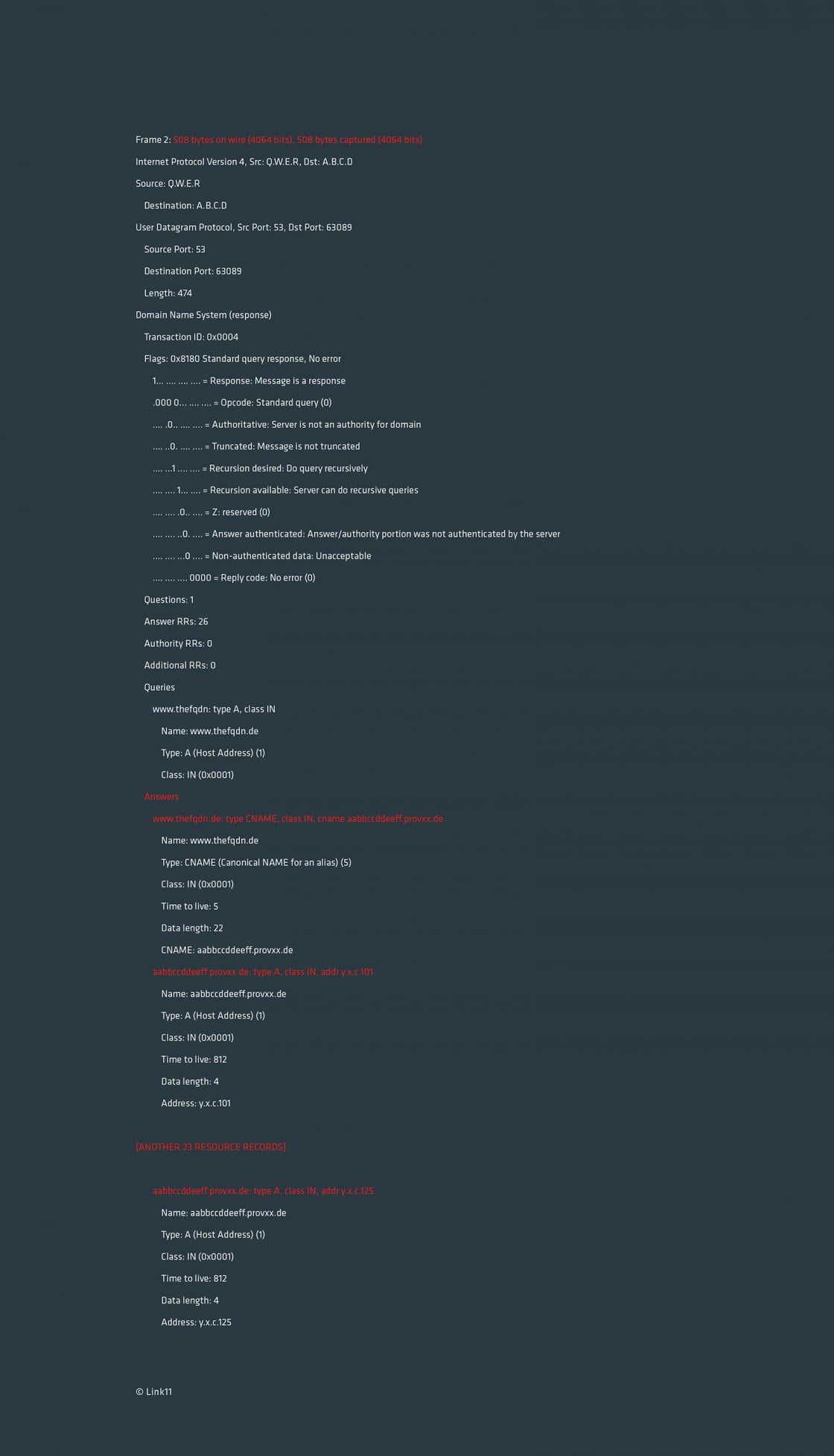
Even a simple request for an A record with a packet size of 74 bytes can lead to a 508-byte reply (an amplification factor of approximately 7). A request and reply like this might look as follows (no layer-2 and layer-3 header shown):
This is what the botnet communication looks like including amplification:
The target faces several threats:
- Internet connection overload
- Overload of the components processing the packets
- Etc.
The worst possible outcome of this type of attack is complete failure of the target’s internet connection.