Some DDoS attacks are loud. Others are large. And still others are one thing above all else: widespread. A recent incident in the Link11 network shows how effective so-called carpet bombing can be. Within just two minutes, not a single server but an entire “/20 network” with more than 4,000 IP addresses was attacked.
What at first glance appears to be a “normal” volumetric attack turns out, on closer inspection, to be a strategically thought-out approach.
What does a /20 network mean?
The term “/20” comes from CIDR notation and describes the size of an IP address range. An IPv4 address consists of 32 bits. If 20 bits are reserved for the network, 12 bits remain for individual hosts. This results in 4,096 IP addresses within this network.
So instead of targeting a single address, such as a web server, in this case the entire address space was attacked. Each of these 4,096 IP addresses received a portion of the attack traffic. This is precisely the core of carpet bombing: the load is distributed broadly across a network segment instead of escalating selectively.
500 gigabits per second – distributed across 4,000 targets
The attack reached a volume of around 500 Gbit/s and lasted only about two minutes. Technically, UDP traffic dominated. The global botnet spanned around 12,000 different IP addresses.
In purely mathematical terms, this means that each individual target IP address accounted for an average of around 100 Mbit/s. Taken on its own, this does not seem unusual. Many modern systems can process significantly more in the short term.
Learn more about a GDPR-compliant, cloudbased and patented DDoS Protection that delivers, what it promises.
But the decisive factor is the shared infrastructure. If these 4,000 addresses are backed by a shared uplink, a data center, or a provider network, the load adds up. Even if each individual address is only moderately loaded, the total capacity of the network connection can be completely exhausted.
The result is comparable to a blocked main water pipe: each individual house may consume only a small amount of water, but if the central supply line is blocked, the faucet remains dry everywhere.
Why carpet bombing is difficult to detect
Precisely because the traffic is distributed, it often appears inconspicuous when viewed in isolation. Individual customers or systems “only” detect increased traffic, but no clearly recognizable DDoS attack. The actual structure only becomes apparent when the entire network is viewed.
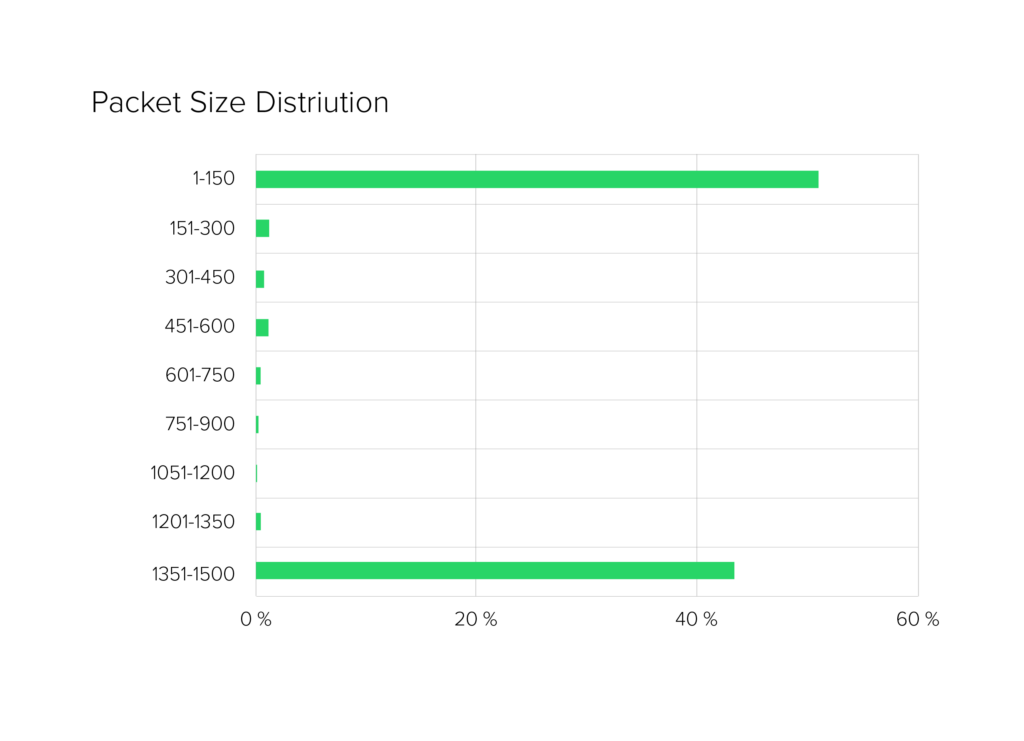
In this case, the distribution of packet sizes was also remarkable. The traffic consisted almost exclusively of very small and very large packets. There was hardly any typical dispersion, as is the case with legitimate applications. Fragmented packets occurred only to a limited extent. Such a binary distribution in terms of packet sizes strongly suggests automated traffic. For systems that rely on behavior and pattern analysis, this can be a clear indicator.
Global botnet structure
The sources of the attack were distributed worldwide. A significant proportion originated in China, with other large portions coming from North America, Europe, and other regions. At the network level, there was also a wide distribution across many autonomous systems.
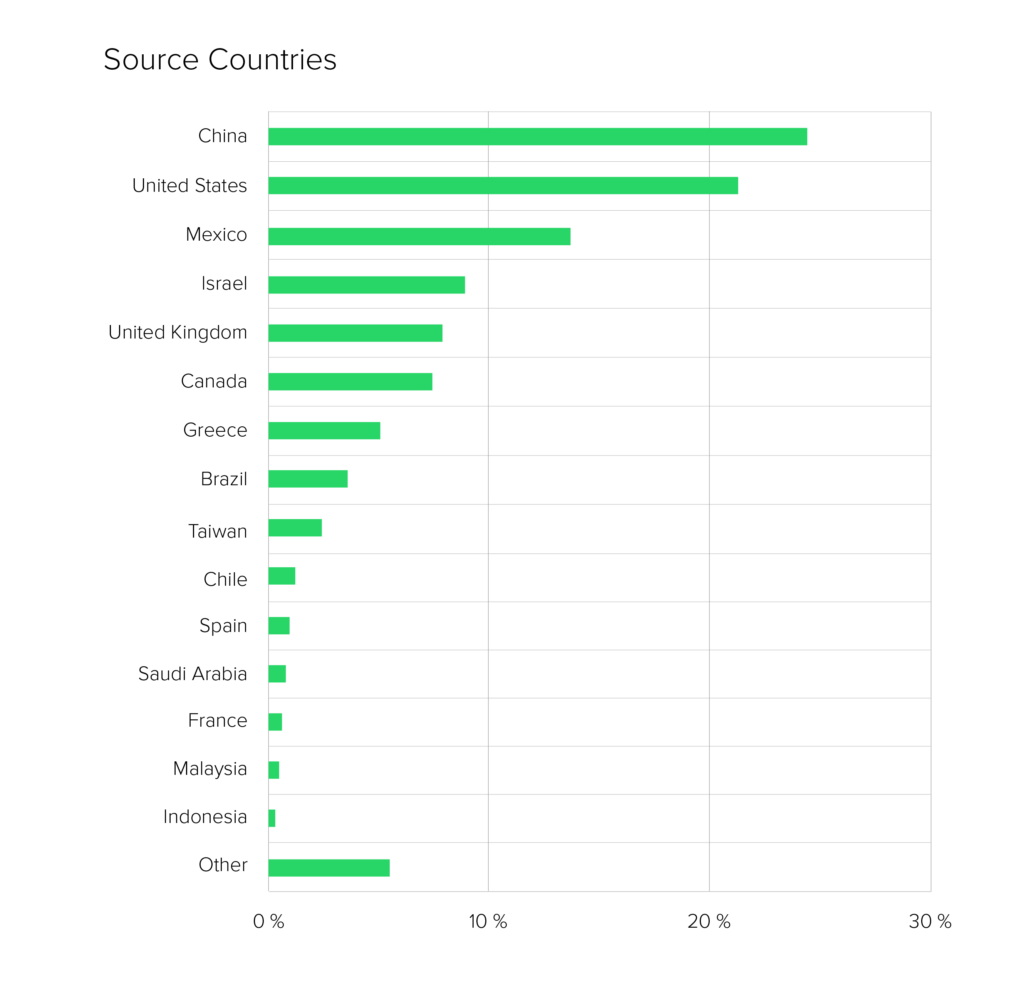
This pattern points to an extensive botnet with a broad geographical reach. Such structures make attribution even more difficult, as the traffic is not limited to individual regions.
At the same time, the geopolitical context is striking. The attacked company is located in a region that has been at the center of international tensions for years. Internal evaluations show that this is not an isolated incident. Comparable attacks have occurred repeatedly at this customer’s site in recent months, some on a similar scale.
In this environment, DDoS attacks are no longer exclusively economically motivated. They serve as a political signal or as an instrument of hybrid warfare.
Two minutes are enough
The short duration of the attack is remarkable. Only a few minutes passed between the start and the end of the DDoS attack. Such “hit-and-run” attacks are not necessarily aimed at long-term overload. Rather, they can be aimed at testing resilience, probing protective mechanisms, or causing selective disruptions.
Their brevity does not make them any less relevant – on the contrary. Short, intense attacks in particular can challenge monitoring mechanisms that are designed for longer periods of time.
Area instead of focus
Carpet bombing illustrates a strategic shift in the field of DDoS attacks. Unlike traditional attacks, which target individual IP addresses or services directly, this method targets the network as a whole.
The load is distributed in such a way that, when viewed individually, it appears harmless, but when added together, it impairs critical infrastructure. Those who only monitor isolated endpoints may only recognize the symptoms, but not the underlying pattern.
The brief attack shows how an entire network segment can be put under pressure. Technically, it was not a record. But the structure makes it clear that modern DDoS strategies no longer rely on spectacular peak values but on intelligent distribution. And that is precisely where their real strength lies.
Take your DDoS resilience to the next level
Carpet bombing is just one of many attack methods that put pressure on modern infrastructures. Learn how Link11 detects and stops complex DDoS attacks in real time.

 Lisa Fröhlich
Lisa Fröhlich