The term DDoSia was first mentioned in October 2022, when the pro-Russian hacker group, NoName057(16), confirmed the existence of the new DDoS project on the social network Telegram. The project itself is considered the successor to the former Bobik botnet that was successfully combated and disbanded in September 2022.
Since then, DDoSia has grown significantly – while there were around 400 members in October 2022, there are now thought to be over 10,000, an explosive increase by a factor of 25. On Telegram, you can see clearly how interest is growing in the topic. Over 45,000 people have now subscribed to the main Russian account. And the trend is still rising.
What exactly is DDoSia?
DDoSia is a toolkit specifically designed by the hacker group NoName057(16) for DDoS attacks and is primarily used for attacks against countries that have expressed criticism of the Russian invasion of Ukraine.
Originally, the DDoSia tool was written in Python and uses CPU threads to launch a large number of network requests at the same time. However, due to the lack of efficiency, the hackers switched from Python to Go. The new Go variants appear to work across platforms, as variants for all major operating systems (Windows, MacOS, Linux, Android) have been discovered. The group is constantly developing the project to make the attacks as effective as possible and proactively thwart potential countermeasures.
The DDoS attacks are organized directly via Telegram in order to bundle targets to ensure the greatest possible damage. Participants are also provided with specially developed malware to download, which is distributed via a ZIP archive and can be deployed at their own discretion. This malware infiltrates computer systems that are already under control in order to use them as additional firepower for the botnet.
In the event of an attack, the IP address is masked with the help of a VPN, which often renders the usual geo-blocking protection measures ineffective. Interested parties are also offered tutorials on how attacks can be implemented as easily as possible and moderators act as a kind of customer service that can be contacted with questions.
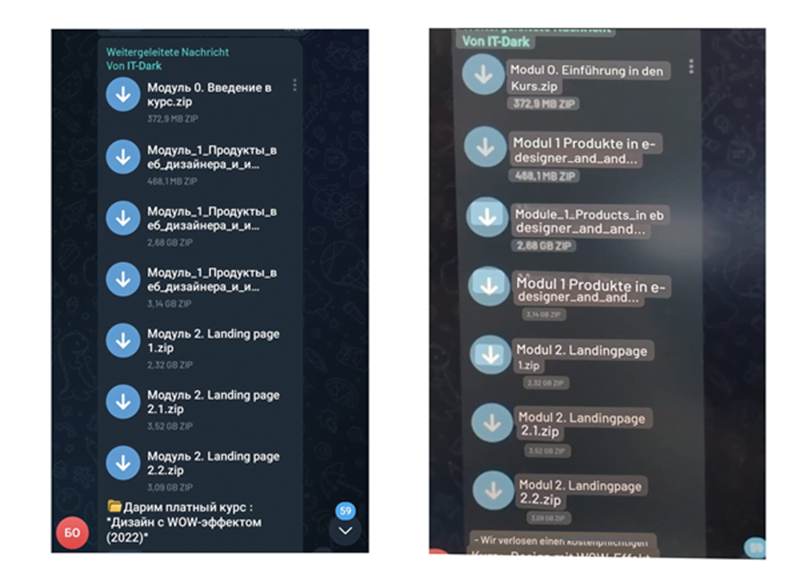
Picture: Tutorials for all participants packaged as a download
In order to constantly expand the botnet and recruit new participants, the hacker group offers a reward in the form of cryptocurrency. Interested parties are assigned a personal ID that is linked to a crypto wallet. Every attack in which the participant is involved makes the digital wallet ring and encourages them to take part in further attacks.
Europe increasingly in the crosshairs
A report by analysts at Sekoia lists 486 websites that were attacked by DDoSia between May and June 2023. On average, almost 15 websites per day were targeted by the botnet. Until June 2023, the group focused on countries in the eastern part of Europe. In addition to Poland and Ukraine, Lithuania in particular was increasingly targeted by the criminal hacker group.
However, the latest data shows the attacks are increasingly moving westwards. In addition to a large number of Italian and French websites, the website of German Foreign Minister Annalena Baerbock, for example, was one of the top 50 most attacked websites. Several websites of German federal authorities or federal states were also the target of attacks. Germany has not yet been one of the main targets. But this situation could change quickly in the future.
The German Federal Office for Information Security (BSI) has now included DDoSia in its annual report “The state of IT security in Germany 2023” and recommends preparing for potential attacks.
DDoSia will not disappear any time soon
As NoName057(16) is constantly developing the DDoS tool and adapting it to different circumstances, it can be assumed that this is a long-term project. Apparently, the group is currently adapting the malware to a large number of other operating systems in order to further expand the target spectrum. This would open the door to significantly more attacks and greater risks.
Another aspect is the growing community, which is also involved in further development and infecting new computer systems, further strengthening the available botnet. It is therefore unlikely that DDoSia will disappear in the near future – in fact, quite the opposite.
Effective protection solutions drastically reduce damage
Specialized and constantly-evolving protection solutions should be the first choice to protect against DDoS threats such as the DDoSia project. If such an option is embedded in a well-thought-out security concept including geoblocking and vulnerability scans, reliable protection can be put in place.
Link11 is prepared for such threat scenarios. Our customers are automatically protected against such attacks without having to make any changes themselves. If you would like to find out more about this topic, please contact one of our security experts. We will be happy to help you with any questions you may have about cyber security and provide you with non-binding advice on effective protective measures.

 Fabian Sinner
Fabian Sinner