Not all DDoS attacks have the same objective. Some are designed simply to overload, while others are intended to conceal something more nefarious. A massive increase in requests immediately raises red flags in every SOC. However, when millions of requests flood the infrastructure in a short period, standard diagnosis often falls short.
At first glance, the case seems clear: a classic DDoS attack designed to cripple availability. But beware of the obvious. A recent analysis of two attack scenarios clearly shows how different the motivation behind seemingly similar traffic can be, and why understanding this distinction is crucial to security strategy.
While one attack merely makes “noise,” the other uses this noise to cover far more dangerous operations.
Case 1: Classic DDoS Attack
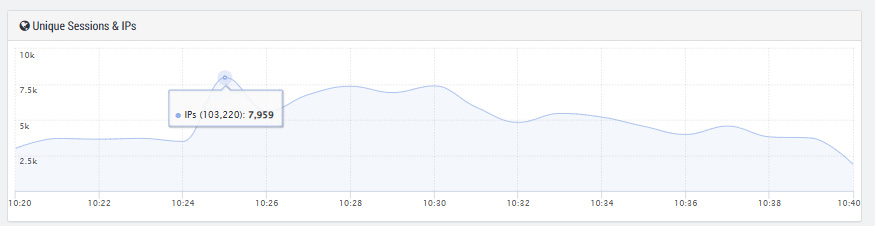
In the first scenario, the login area was bombarded with approximately 16 million requests. Several thousand IP addresses primarily targeted the root domain.
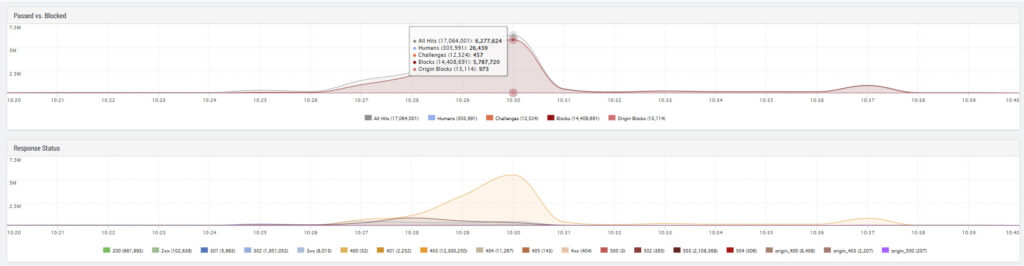
From a technical perspective, this was a “clean” attack, albeit one involving a massive volume of traffic.
The forensic indicators were clear:
- Pure traffic overload to exhaust resources.
- DDoS signatures that triggered immediate rate limits.
- No evidence of SQL injection or cross-site scripting (XSS) attempts.
Such attacks are loud and highly visible. They are designed to tie up or completely overwhelm backend resources. Without upstream protection mechanisms, a botnet of this size can push critical applications to their limits and cause massive outages.
Learn more about an easy-to-implement and highly effective WAAP solution.
Everything from a single source, and available as a fully managed service upon request.
This is the “classic” DDoS dynamic. With a modern WAAP (Web Application and API Protection) platform, however, the effect is limited. IP addresses are automatically blocked, rate limits are precisely applied, and the attack fizzles out as filtered background noise.
Case 2: DDoS as a Smokescreen
The second scenario was technically similar but strategically far more insidious. In this case, two domains, including a popular booking platform, were targeted simultaneously. With a volume of 14 to 40 million requests, the intensity was higher than in the first case.
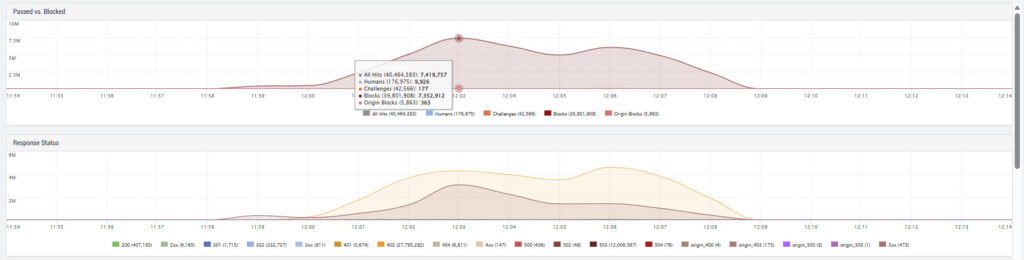
Further analysis of the web application firewall (WAF) revealed an additional dangerous pattern: targeted signatures for SQL injections and cross-site scripting (XSS).
Excerpt from the WAF Analysis:
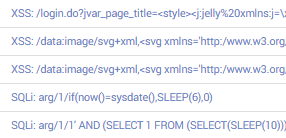
This pattern suggests a “smokescreen” attack. The logic behind it is as simple as it is dangerous.
- The noise: A massive DDoS attack creates operational chaos, floods monitoring systems with alarms, and inflates log files enormously.
- The camouflage: In the slipstream of this noise, attackers attempt to quietly and precisely place exploits, hoping they will be lost in the mass of error messages.
In this case, though, the attackers failed due to their own miscalculation. They used the same IP addresses for the volumetric DDoS attack and the infiltration attempts. These addresses were already blocked by the DDoS protection rules before the SQL or XSS attempts could be made.

This approach was not technically sophisticated; a more experienced actor would have used separate infrastructures and IP pools. Nevertheless, the intention was clear. This is precisely where the crucial difference from a pure volume attack lies. While case 1 focused on disruption, case 2 aimed to compromise the system. This is a risk that comes with solutions focusing solely on security and lacking intelligence.
The strategic difference
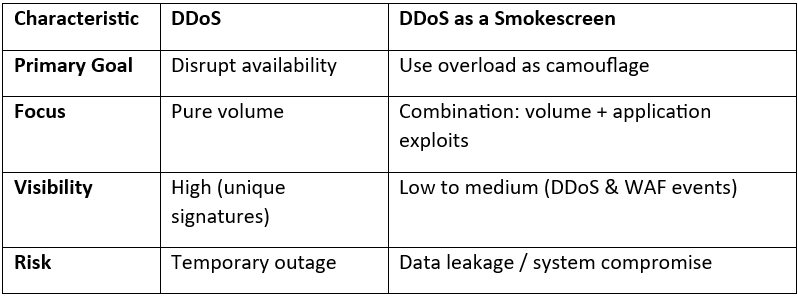
In the second case, if the company had only used isolated DDoS protection without integrated WAF intelligence, the “smoke” would have been filtered out. However, the fine needle pricks of the SQL injections could have reached the backend systems.
The decisive factors were:
- Automated IP quarantine: An IP address that stands out due to DDoS patterns is immediately blocked globally.
- Cross-domain reputation: Knowledge of a malicious IP address on Domain A immediately protects Domain B.
- Holistic view: Security teams recognize the entire attack pattern, not just the “storm.”
Conclusion
Not every traffic peak is solely a capacity issue. In a hybrid threat landscape, a DDoS attack often serves as a distraction for other processes taking place. Focusing solely on bandwidth can cause you to overlook the actual risk. Today, resilience means more than just staying online: it also means decoding attacks in their entirety.
Would you like to learn how a modern WAAP architecture correlates DDoS and application attacks in real time and stops them fully automatically? Learn more about Link11’s holistic protection solutions now.

 Lisa Fröhlich
Lisa Fröhlich