DDoS protection is not a “one size fits all” product, and in the event of an attack, the pressure to find a solution increases. Often, it’s a matter of an ad hoc available – in doubt, any – solution. Unfortunately, an unsuitable solution provides minimal protection at best and at worst, victims of a DDoS attack are offline until it is removed.
Link11 offers two different DDoS protection solutions: Infrastructure Protection and Web Protection. Both were developed with very different implementations in mind. As their names suggest, Infrastructure DDoS Protection and Web DDoS Protection are each designed for their specific use case: protecting against DDoS attacks on OSI layers 3-4 or protecting all web applications.
Artificial intelligence filters traffic
In both services, traffic is redirected to a Link11 scrubbing center. In this data center, live traffic flows through multiple layers of protection including AI-based filtering. Once DDoS filtering is complete, only legitimate traffic is routed.
Both protection systems can be configured as “Always On” or “On Demand.” The difference between these two options is when the redirection to the scrubbing center occurs.
“Always On” means that the service is permanently redirected. As soon as the traffic only flows through the scrubbing center in the event of an attack, it is the “On Demand” configuration. For full protection against DDoS attacks, the permanent redirection as “Always On” is particularly suitable. This provides immediate protection against all attacks. In addition, the underlying AI provides significantly more data, on which it can train, for the system to be protected.
Broad protection on the ground: Infrastructure DDoS Protection
Infrastructure DDoS Protection is designed specifically for network protection. It operates on the third and fourth layers of the OSI model, also known as the transport layer, and is therefore also referred to as Layer 3 protection. Since it is a Layer 3 solution, the instances are based on IPs. This has the advantage that they provide the same protection regardless of the protocols used at higher layers. That is, the same instance can protect routers, web servers, mail servers, VPN gateways, or any other device that works with the IP protocol.
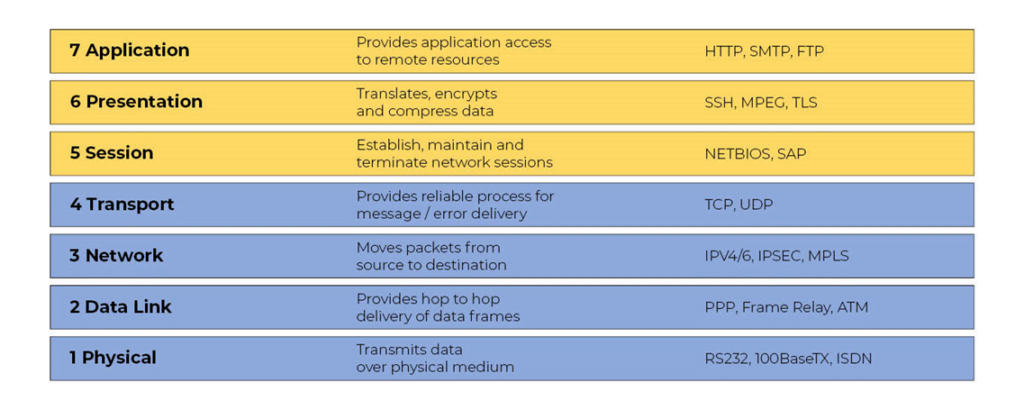
The different layers in the OSI model
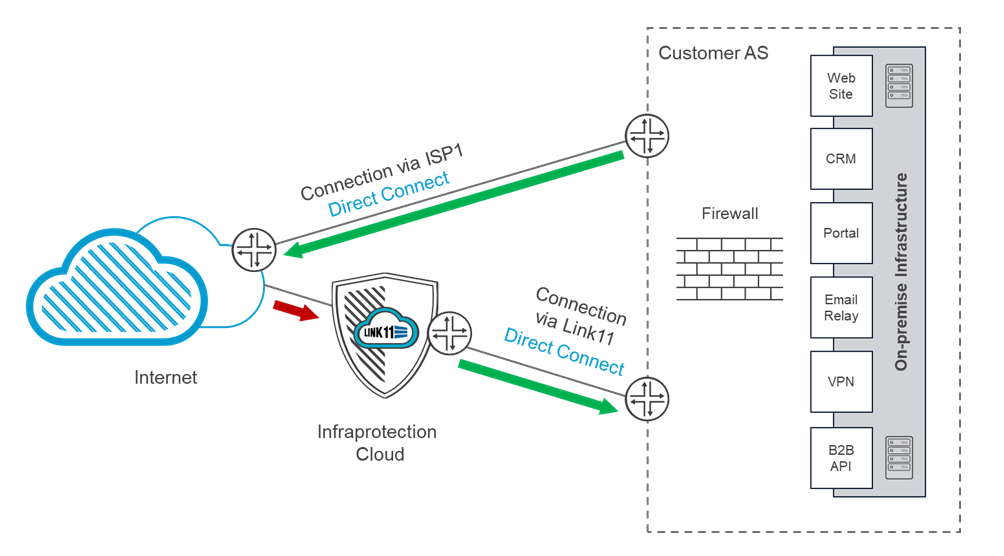
Traffic is redirected using the BGP protocol. This means that each instance can protect at least 254 devices (/24 announcement). This BGP announcement should be the most specific route for the IPs. In other words, the route that is best defined so that all traffic for the IPs is routed to the Link11 scrubbing centers. The traffic comes back via an asynchronous route because it does not need to flow through Link11 again. Thus, the malicious traffic is routed to the Link11 backbone and cleaned there. As a result, nothing needs to be changed in the customer’s network in terms of routing.
BGP protocol: How the traffic flows
Secure web applications with Web DDoS Protection
Unlike infrastructure protection, Web DDoS Protection provides Layer 7 protection for each individual HTTP(S) application. Each instance is specifically tailored to the application and provides protection against threats at all levels. This includes attacks via code injection such as SQL injection and cross-site scripting (XSS) as well as DDoS attacks.
Traffic is redirected via the Domain Name System (DNS). After the service is provisioned, a virtual IP (VIP) is assigned to serve as a secure IP for the application’s DNS A record. Incoming traffic is filtered, and legitimate requests are forwarded to the originating servers.
Unlike the infrastructure protection solution, the filtered data from the origin is first forwarded to Link11 and then to the user. The latter expects a response from the virtual IP address to which the request was sent. This synchronous flow of traffic back also prevents an attacker from learning the true IP of the sender.
Typical risks according to the OSI model
Threats can be classified using the OSI layer model in a similar way to the two protection systems. For this, threats are related to the protocols or technologies they target. Flood-style attacks such as UDP flood are referred to as layer 3 attacks, and that despite UDP being a layer 4 protocol. Each UDP message requires an IP packet. This results in a flood of IP packets when an attack occurs, allowing such a cyberattack to be immediately detected and prevented at OSI layer 3.
Another well-known layer 3 protocol for DDoS attacks is ICMP. The Internet Control Message Protocol is used, for example, in the “Ping of Death” and “Smurf attacks.” Meanwhile, most modern network devices are no longer vulnerable to these attacks. At the same time, ICMP data packets can be easily generated to overwhelm an unprotected network.
If application protocols HTTP are the focus of attackers, the threats target layer 7 of the OSI model. Although the so-called flooding attacks on Layer 7 are still seen, more sophisticated attacks are now occurring. These attacks can consume server resources with minimal increase in traffic.
Such attacks as “slowloris,” which block the availability of a Web server, consume server resources by attacking Web servers directly. In this attack, named after a primate (Loris) that lives in Asia and is very slow, connections to the server are opened and kept open until the server’s resources are exhausted. This is done without causing a noticeable increase in Layer 3 traffic.
Making the most of DDoS protection
The key to getting the most out of a DDoS protection solution is understanding how well it fits the environment and what threats users are vulnerable to. Before looking at a DDoS defense system, you should first create a list of critical systems and an outline of the components required to keep them running.
This should include exactly which protocols and application layers you need to protect, or at least at which layer of the OSI model these systems operate. Then consider how much downtime you can tolerate for these systems and applications and define it accordingly in your SLA. Once you know exactly what level of protection is needed for which devices, you can find and select the right DDoS protection solution for your systems so that all systems are extensively protected.
Do you have questions about infrastructure protection, secure web applications or need help identifying the right DDoS solution? Our colleagues would be happy to support you in a one-on-one conversation.

 Fabian Sinner
Fabian Sinner