Web Application and API Protection (WAAP)
Unified security platform that blocks DDoS and other threats while preventing downtime, reputational damage, and financial loss.







LEADING COMPANIES WORLDWIDE ALREADY TRUST IN OUR SOLUTIONS –
BE ONE OF THEM
The Link11 Cloud WAAP platform delivers comprehensive, multi-layered protection for essential web assets. Web applications, and APIs are protected around the clock – maximizing service availability, optimizing performance and providing peace of mind.
Our proven combination of Web Application Firewall, Web DDoS Protection, Bot Management, and API Security already safeguards millions of web applications and APIs for medium-sized businesses and enterprises worldwide.
The digital threat is multifaceted, and effective defense is more important than ever
-
32%
of global internet traffic is
caused by unwanted “bad bots. -
40%
of all companies surveyed have been the
victim of an API attack in the last 12 months. -
1
Web DDoS attacks have overtaken
ransomware in Europe.

How you benefit from Link11 WAAP
-
Unified Solution for All WAAP Pillars
An all-in-one platform that combines all functions in a single pane of glass, which also solves the problem of having to deal with different vendors during an attack. This is not only a lot easier, but also saves you time, money, and resources
-
Precise Security
The system is highly accurate, distinguishing seamlessly between legitimate and non-legitimate traffic. This precision reduces false positives and false negatives, improving the detection of attacks without blocking the legitimate traffic.
-
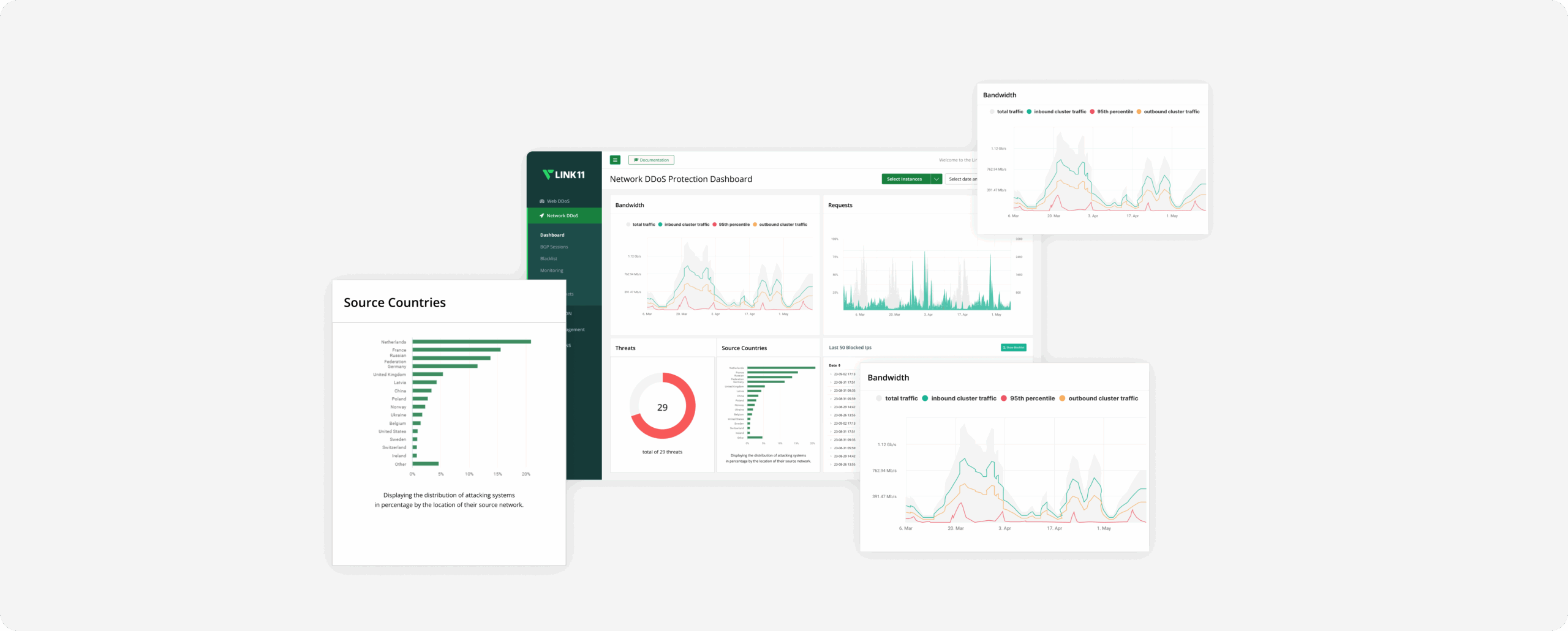
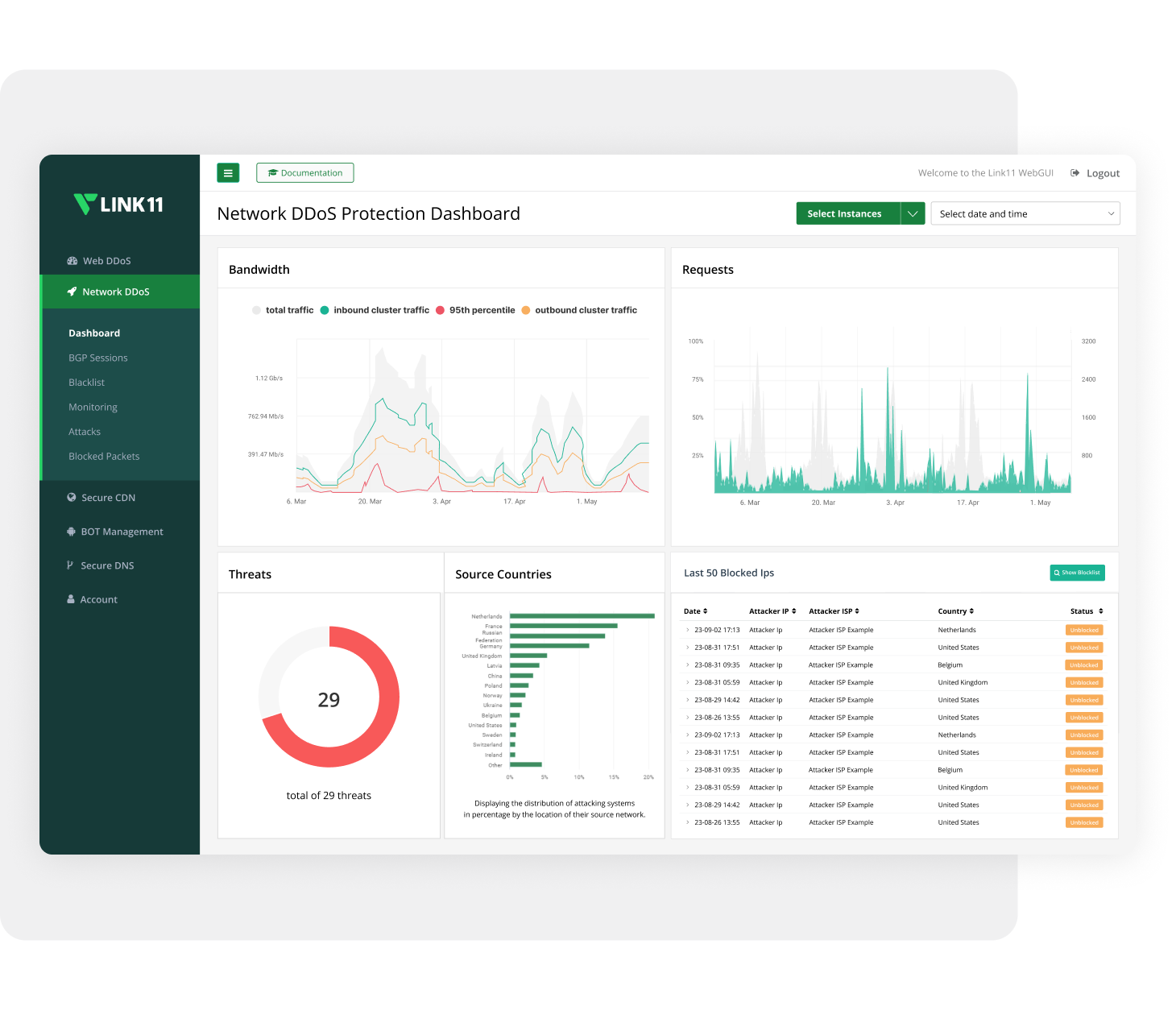
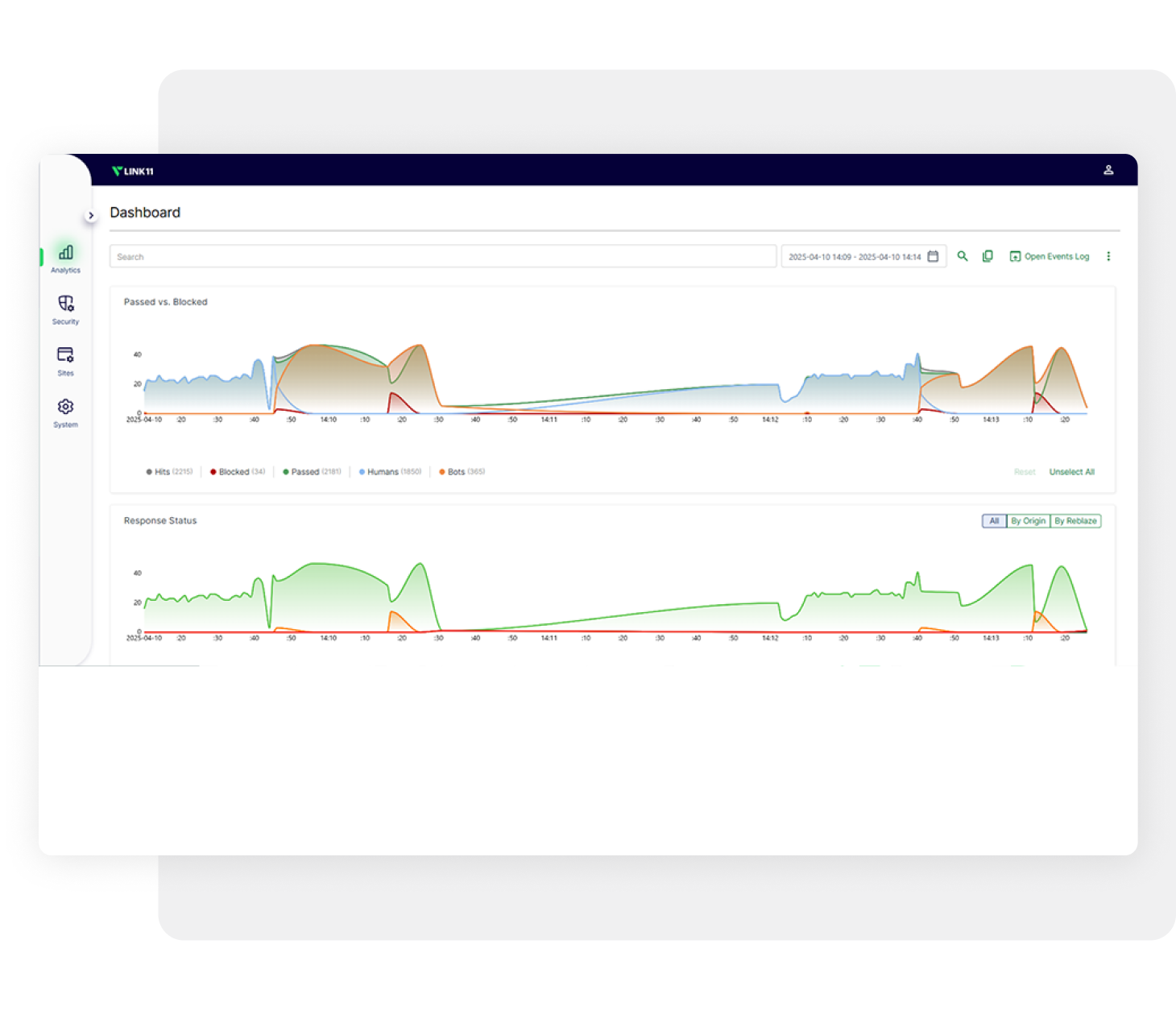
Real-Time Traffic Monitoring
The platform automatically protects you and provides full visibility of all incoming traffic in real time- not just the blocked traffic. Additionally, it provides visibility to all parts of the http/s request, making it easier to investigate attacks. This ensures you‘re always in control, enabling effective detection, investigation, and adjustment of security rules as needed.
-
Understand how AI uses your service
Not every automated request is an attack. The AI Management Dashboard detects AI systems separately from bots. Shows who extracts data and who sends users back, and lets you allow, limit, or block access. Every request is logged, giving security teams compliance, and legal teams a clear basis for decisions.
-
Fully Managed Service
Our fully managed solution, maintained by security experts around the clock, ensures your protection is always up to date—24/7, 365 days a year. You‘re covered, guaranteed.
-
Deploys Anywhere
Link11’s WAAP integrates seamlessly with all modern architectures — whether private or public cloud, single or multi-cloud, hybrid, or on-prem solutions. The platform is quick to deploy and easily adaptable to any use case, offering protection for web apps & APIs wherever they’re hosted. In addition, Link11’s WAAP includes a dedicated solution to protect mobile app traffic, leveraging a proprietary mobile SDK technology.
LINK11 WAAP – FOUR SOLUTIONS IN ONE CUTTING-EDGE PLATFORM
As cyberattacks become more sophisticated and security talent becomes scarcer, a streamlined, user-friendly
solution is essential. With our cloud based WAAP, you get four robust security products in a unified platform
in a single pane of glass.
Web Application Firewall
Our Web Application Firewall (WAF) protects against all vulnerabilities listed in the OWASP Top 10, as well as threats such as: Code and SQL Injection, Cross-Site Scripting and Malicious Payloads. Unlike traditional approaches that rely solely on signature detection and IP blocking, Link11’s WAF includes advanced defenses such as allowed application enumeration and granular access controls (ACLs).
Bot Management
Link11 provides a platform with powerful Bot Management that filters unwanted bot traffic before it reaches your applications or APIs. Our solution prevents data theft, scraping, credential stuffing, brute force attacks, application abuse, vulnerability scanning and inventory theft and protects your systems from unwanted access and disruption.

Web DDoS Protection
Link11 provides comprehensive protection against Layer 7 DDoS attacks. Web DDoS Protection provides protection against a wide range of DDoS attack methods, including HTTP floods, Slowloris attacks, application-specific attacks and zero-day vulnerability exploitation.

API Security
APIs are common targets due to their widespread use and often inconsistent maintenance. Link11’s API protection closes these security gaps and provides comprehensive protection for your web-based APIs. Our solution protects against a wide range of API attacks, including the OWASP Top 10 API security risks.
-
Self-Onboarding · Live in 30 min.
CoreFor small teams and projects that need reliable performance without extra hassle.613 € /monthplus VAT · Cancelable monthly490 € /monthplus VAT · Cancelable monthly-
2domains*
-
10ratelimit rules
-
7-day logs
-
-
Best Choice
Self-Onboarding · Live in 30 min.
AdvancedFor growing platforms with increasing data traffic and rising risks.988 € /monthplus VAT · Cancelable monthly790 € /monthplus VAT · Cancelable monthly-
5domains*
-
50ratelimit rules
-
14-day logs
-
-
Managed · Personal Onboarding
EnterpriseEnterprise-grade security for business-critical infrastrucutre where downtime is not tolerated.CustomizedPricing based on your needsCustomizedPricing based on your needs-
∞domains
-
∞rules
-
Custom– up to 5 years
-
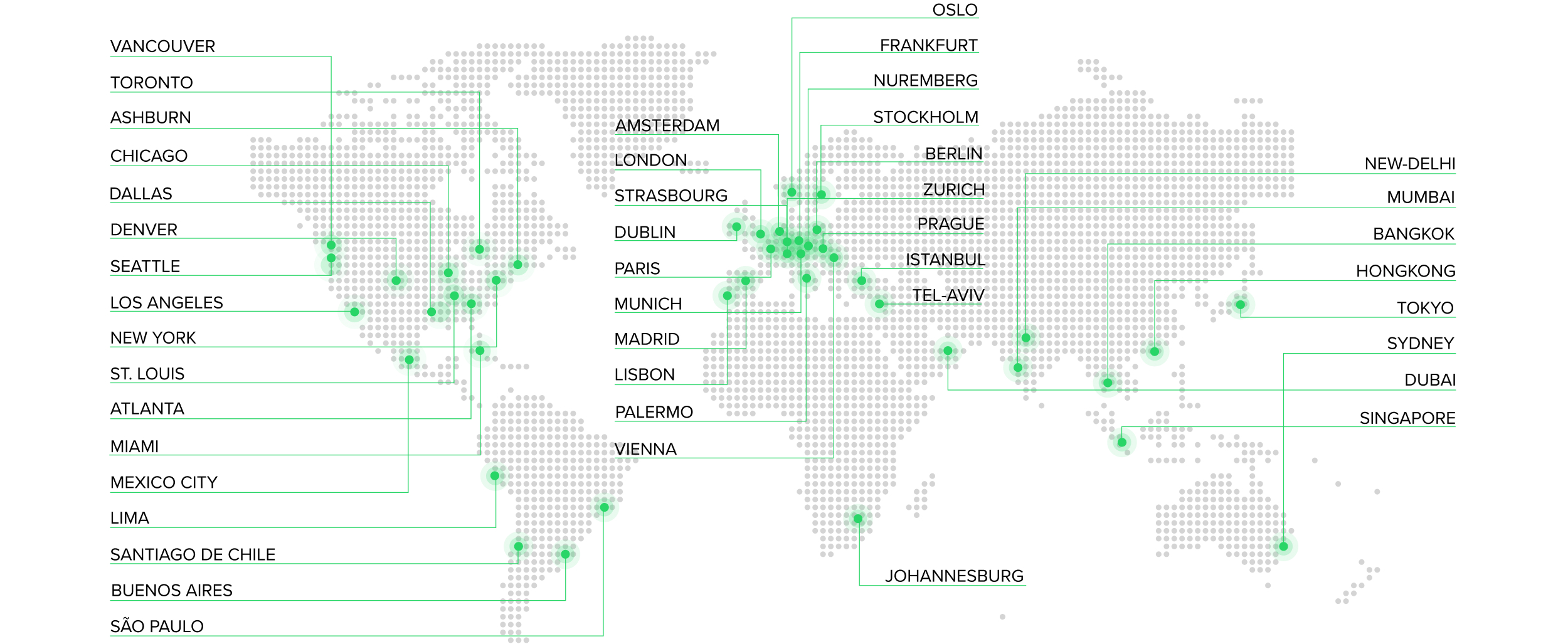
THE GLOBAL LINK11 CLOUD INFRASTRUCTURE
-
13
Scrubbing Centers
-
43
Edge POPs
-
107
Cloud POPS